Emsisoft Decryptor for RedRum 1.1.0.0
|
Author:
Emsisoft
Date: 07/31/2020 Size: 1.71 MB License: Freeware Requires: 10|8|7 Downloads: 1799 times Restore Missing Windows Files |
Emsisoft Decryptor for RedRum was designed to help decrypt files locked by the RedRum strain of ransomware.
RedRum encrypts your files using AES256 GCM and RSA-1024, adding the extension ".id-.[].redrum" to files.
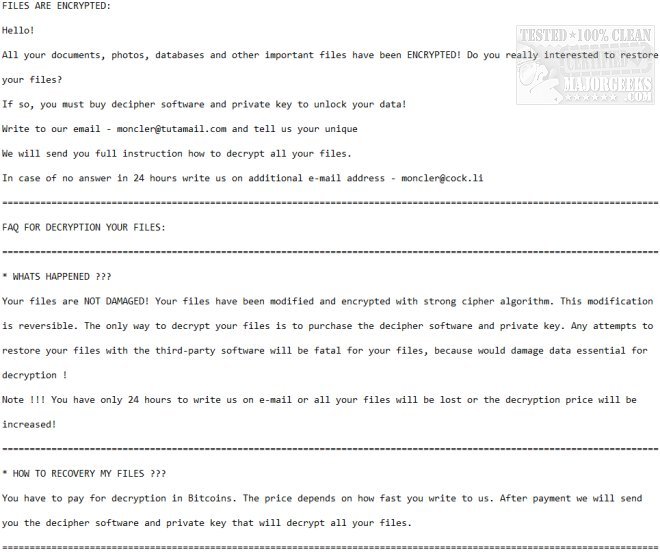
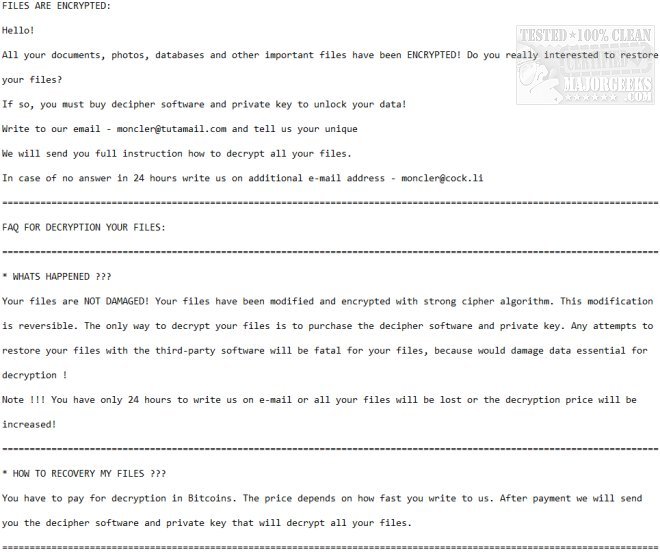
The ransom note "decryption.txt" will have similar text to what is shown below:
You will need to remove the malware from your system first; otherwise, it will repeatedly lock your system or encrypt files. By default, Emsisoft Decryptor for RedRum will pre-populate the locations to decrypt with the currently connected drives and network drives. Additional locations can be added via the Add button.
Emsisoft Decryptor for RedRum requires access to a file pair consisting of one encrypted file and the original, unencrypted version of the encrypted file to reconstruct the encryption keys needed to decrypt the rest of your data. Do not change the file names of the original and encrypted files. This fact is because the decryptor may perform file name comparisons to determine the correct file extension used for encrypted files on your system.
Run the RedRum decryptor, and select your file pair. Then click the Start button. The decryptor will start to reconstruct the required encryption parameters. Depending on the ransomware and your computer, this process can take a significant amount of time.
Emsisoft Decryptor for RedRum will inform you that the decryption process is complete. If you require a report for your records, you can save it by clicking the Save Log button. You also have the option to copy it straight to your clipboard for use in emails, forum posts, etc., if needed.
Similar:
Which Anti-Malware App Is Best and Can It Run Alongside My Antivirus
What's the Best Antivirus and Is Windows Defender Good Enough?
Windows Device Performance & Health Explained
How to Tell the Difference Between a Virus and a False Positive
How to Manage Windows Defender Antivirus Found Threats
What to Do When Your Norton or McAfee Antivirus Expire
RedRum encrypts your files using AES256 GCM and RSA-1024, adding the extension ".id-.[].redrum" to files.
The ransom note "decryption.txt" will have similar text to what is shown below:
You will need to remove the malware from your system first; otherwise, it will repeatedly lock your system or encrypt files. By default, Emsisoft Decryptor for RedRum will pre-populate the locations to decrypt with the currently connected drives and network drives. Additional locations can be added via the Add button.
Emsisoft Decryptor for RedRum requires access to a file pair consisting of one encrypted file and the original, unencrypted version of the encrypted file to reconstruct the encryption keys needed to decrypt the rest of your data. Do not change the file names of the original and encrypted files. This fact is because the decryptor may perform file name comparisons to determine the correct file extension used for encrypted files on your system.
Run the RedRum decryptor, and select your file pair. Then click the Start button. The decryptor will start to reconstruct the required encryption parameters. Depending on the ransomware and your computer, this process can take a significant amount of time.
Emsisoft Decryptor for RedRum will inform you that the decryption process is complete. If you require a report for your records, you can save it by clicking the Save Log button. You also have the option to copy it straight to your clipboard for use in emails, forum posts, etc., if needed.
Similar:
 Screenshot for Emsisoft Decryptor for RedRum
Screenshot for Emsisoft Decryptor for RedRum





 Tactical Briefings
Tactical Briefings